Capella alliance
Co-Creating Tomorrow, Today
Join Capella Alliance and shape the future of technology collaboration.

Power Your Progress!
Leverage Nisum as your global IT services platform to grow your customers.
Create new opportunities with collaborative engagements
Co-Opete
To satisfy existing but unanswered customer needs
Co-Innovate
To create an entirely new type of business and market
Co-Market
Bring new technologies, products and services to customers
What is Capella Alliance?
Nisum’s Capella Alliance is a dynamic network of industry leaders and experts united by a common goal – driving revenue growth, innovation, and excellence in the tech landscape.
With Nisum’s delivery footprint across nine global economies, our members join forces on innovative projects, unlocking opportunities with new and current clients.
Capella cultivates a dynamic and vibrant ecosystem, creating new service areas, extending customer life, fostering innovation, driving revenue growth, and expanding addressable markets.
Our members, spanning diverse domains, collaboratively shape the future through strategic partnerships, cutting-edge technologies, and shared expertise.
Who can join ?
Capella Alliance is open and invites a diverse array of potential members. We welcome those who aspire to unlocking fresh revenue streams, and co-creating innovative solutions. Embrace the opportunity to shape the future of technology and business with us.

Are you an Entrepreneur, Startup, SMB?
Empowering entrepreneurs, tech startups; partnership for unparalleled success
Are you a Business Management Consultant?
Excellence in innovation, unleash new opportunities, collaboration for mutual success.

Do you offer IT Solutions and services?
Elevate your business, unlock new horizons, embrace IT success.
Are you a Subject Matter Expert?
Thrive together, unlock growth, explore new avenues, earn commissions.
Are you a Sales, Marketing Specialist?
Collaborative journey, create income, impact, endless possibilities await.
Are you a Reseller, Integrator, agency?
Where possibilities meet, explore new opportunities, embark on success.
1
Express Your Interest
Fill out a simple expression of interest form, and our team will reach out to you.
2
Qualification and Approval
Our team will guide you through pre-qualification, approval, and agreement.
3
Embark on The Journey
We'll swiftly initiate onboarding to explore exciting opportunities with Capella Alliance.
How will it work for me?

Collaborative Partnership
Nisum Delivers With You
- Establish a collaborative delivery team.
- Share both risk and reward.
- Capella PMO ensures efficient project orchestration.
Goal-Oriented Engagement
Nisum Delivers for you
- Let Nisum deliver on your behalf.
- Receive a fixed referral fee for your participation.
- Leverage Capella PMO for streamlined project management.
Explore New Revenue Avenues
Co-create success with Capella Alliance. Access untapped markets and unlock fresh revenue streams.
Why Join?
Win more customers with the Capella Alliance.
Our portfolio of experienced technology resources, and industry-leading solutions, will help you grow faster
- Unlock Growth
- Access to Innovation
- Co-Branded Marketing
- Revenue-Sharing
- Technology partnerships
- Seamless Collaboration
- Dedicated Support
- Smooth Processes
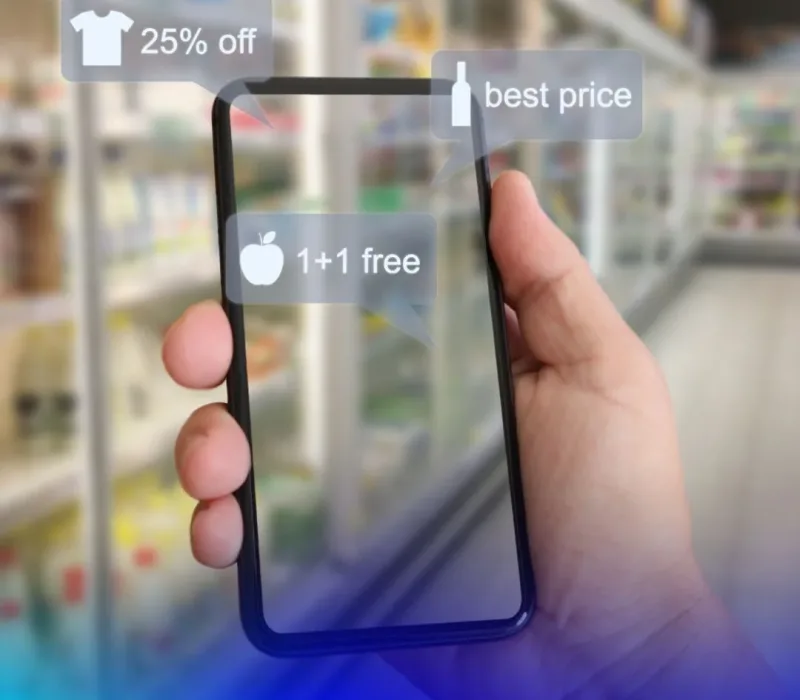
Elevate Your AI & ML Initiatives
Are you missing out on AI & ML opportunities due to a skills gap?
Nisum is your gateway to unlocking the full potential of transformative technologies.
Our expertise in AI & ML, coupled with a network of seasoned professionals, empowers you to take on innovative projects with confidence.
From strategic planning to flawless execution, Nisum ensures you have the right support to make the most of AI & ML opportunities. Let’s propel your business forward, together.
AI & ML
Custom Development
DevOps Support
Testing & QA
Insights & Analytics
Cloud services
Global team
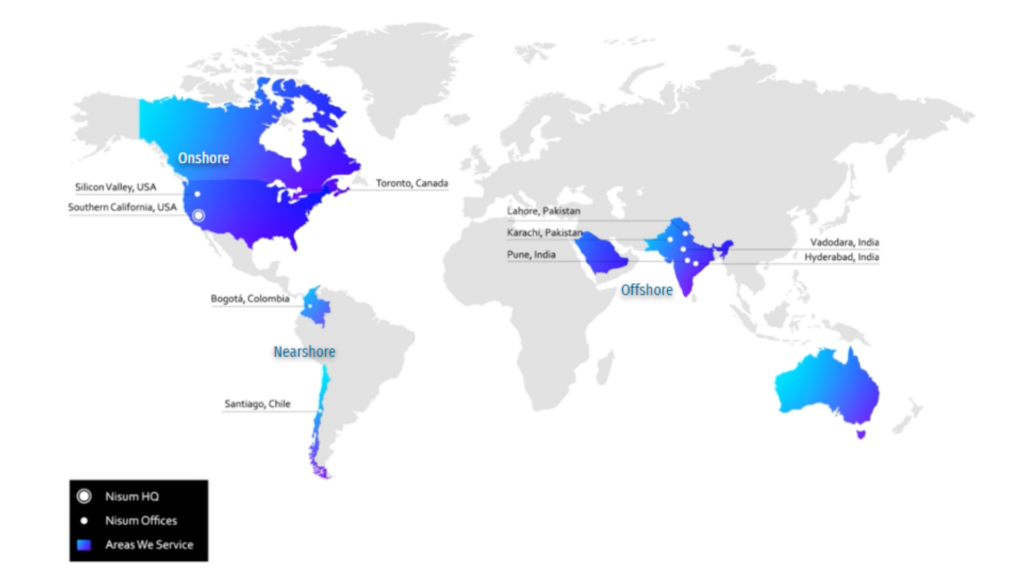
Countries
Offices
Employees
Delivery Guaranteed
Discover New Horizons
Tools & Technologies



Solutions Tailored to Your Challenges
Overcome Project Delivery Challenges, Achieve Your Goals
Fill Your IT Resourcing Gaps With Top Experts
Keep projects on track with a complete team. Access top IT talent globally through our extensive delivery platform.
Speed Up Delivery, And Reduce Time To Market
Accelerate time-to-market with Capella. Optimize resources and ensure timely project delivery.
Gain Time To Focus On Your Core Business Growth
Stay focused on your core business. Let the Nisum Capella team deliver for you.

Technical Excellence Guaranteed
- AI & ML Engineering
- Data Science, Insights, Analytics
- DevOps, Information security
- Quality Engineering & Automation
- Program & Agile Project Management
Join the Capella Alliance Network
Become a member and tap into exclusive opportunities. Elevate your business with Capella’s strategic collaboration.